How Schnorr Signatures Strengthen Blockchain Security

Schnorr Signature is a revolutionary cryptographic algorithm that has gained significant attention in recent years. Its unique design and advanced features make it a powerful tool in the world of cybersecurity. In this comprehensive guide, we will explore the basics of Schnorr Signature, its advantages, its role in cryptography, its future prospects, and how to implement it effectively. So fasten your seatbelts as we embark on an exciting journey into the world of Schnorr Signature!
Understanding the Basics of Schnorr Signature
If you are new to the world of cryptography, understanding the basics of Schnorr Signature is a great place to start. So, what exactly is Schnorr Signature and how does it function? In simple terms, Schnorr Signature is a digital signature scheme that allows users to sign and verify the integrity of messages or transactions in a secure and efficient manner.
Definition and Function of Schnorr Signature
Schnorr Signature was first introduced by Claus Schnorr in 1989 and has since become a prominent player in the field of cryptography. It offers a mathematical means to verify the authenticity and integrity of digital information.
But let's dive a little deeper into how Schnorr Signature actually works. When a user wants to sign a message or transaction, they generate a random value known as a nonce. This nonce, along with the user's private key, is used to compute a point on an elliptic curve. This point is then combined with the message or transaction to create a signature.
Now, when someone wants to verify the signature, they take the signature and the corresponding public key of the signer. Using the same elliptic curve, they compute a point and compare it to the one derived from the signature. If the two points match, the signature is considered valid.
Unlike traditional signature schemes, Schnorr Signature provides additional security by utilizing elliptic curve cryptography. This makes it much more resistant to various types of attacks, such as forgery and tampering.
The Mathematical Principles Behind Schnorr Signature
At its core, Schnorr Signature relies on the mathematics of elliptic curves and discrete logarithm problem. Without delving too deep into the complexities, let's just say that these principles form the foundation of the security provided by Schnorr Signature.
Elliptic curves are mathematical structures that have unique properties, making them suitable for cryptographic purposes. The discrete logarithm problem, on the other hand, is a mathematical challenge that involves finding the exponent used to generate a given point on an elliptic curve. This problem is believed to be computationally hard, which adds to the security of Schnorr Signature.
By utilizing these mathematical concepts, Schnorr Signature ensures that each signature is unique and cannot be forged or tampered with. This makes it an ideal choice for applications that require high-level security, such as blockchain technology and digital identity verification.
The Advantages of Schnorr Signature
Now that we have a basic understanding of Schnorr Signature, let's explore its advantages over traditional signature schemes.
Enhanced Security Features
Schnorr Signature offers enhanced security features compared to traditional signature schemes, making it more resistant to attacks. Its elliptic curve cryptography provides a higher level of security, ensuring the integrity and authenticity of digital information.
Furthermore, Schnorr Signature also provides robust protection against quantum-based attacks, which are becoming a growing concern in the field of cryptography.
One key security advantage of Schnorr Signature is its resistance to side-channel attacks. These attacks exploit information leaked during the computation of a cryptographic algorithm, but Schnorr Signature's design minimizes such vulnerabilities, enhancing overall security.
Efficiency and Scalability
In addition to its strong security features, Schnorr Signature boasts remarkable efficiency and scalability. Its compact signature size and fast verification process make it ideal for applications with limited computational resources.
Moreover, Schnorr Signature supports multi-signatures, allowing multiple individuals to sign a single document or transaction. This greatly simplifies complex approval processes, saving time and resources.
Another aspect that contributes to the efficiency of Schnorr Signature is its simplicity in key generation and signing processes. This simplicity not only speeds up cryptographic operations but also reduces the chances of implementation errors that could compromise security.
The Role of Schnorr Signature in Cryptography
Schnorr Signature has found widespread use in various fields of cryptography. Let's explore two prominent areas where Schnorr Signature plays a crucial role.
Schnorr Signature in Blockchain Technology
The decentralized nature of blockchain technology demands secure and efficient signature schemes. Schnorr Signature perfectly fits the bill by providing enhanced security, scalability, and efficiency.
By adopting Schnorr Signature, blockchain platforms can significantly improve their transaction speed, reduce storage requirements, and enhance the overall security of the system.
Schnorr Signature in Digital Identity Verification
In the digital era, establishing and verifying digital identities is of paramount importance. Schnorr Signature offers a robust solution to this challenge, ensuring the integrity and authenticity of digital identities.
With Schnorr Signature, the process of verifying digital identities becomes more secure and streamlined. This has great implications in various sectors, including banking, e-commerce, and government services.
The Future of Schnorr Signature
The future looks bright for Schnorr Signature as it continues to gain traction in the world of cryptography. Let's take a glimpse into what lies ahead.
Potential Developments and Improvements
Researchers and developers are constantly exploring ways to improve Schnorr Signature further. Potential developments include optimizing signature size, enhancing key management, and further strengthening the security against emerging threats.
As Schnorr Signature evolves, we can expect to see more efficient and secure cryptographic systems based on its principles.
Challenges and Solutions for Widespread Adoption
Like any emerging technology, Schnorr Signature faces its fair share of challenges in achieving widespread adoption. One of the significant hurdles is the need for standardization and compatibility across different platforms.
Efforts are already underway to address these challenges and develop frameworks that ensure seamless integration of Schnorr Signature into various cryptographic systems.
Implementing Schnorr Signature
Now that we have covered the basics and advantages of Schnorr Signature, let's dive into its implementation.
Step-by-Step Guide to Using Schnorr Signature
Implementing Schnorr Signature may seem daunting at first, but fear not! We have compiled a step-by-step guide to help you successfully integrate Schnorr Signature into your cryptographic applications.
- Choose an appropriate programming language and cryptographic library that supports Schnorr Signature.
- Generate a public-private key pair using elliptic curve cryptography.
- Create the message or transaction that needs to be signed.
- Sign the message using your private key.
- Share the signed message and your public key with the intended verifier.
- Verify the signature using the provided signed message, the public key, and the original message.
Best Practices and Common Mistakes to Avoid
Implementing Schnorr Signature effectively requires following best practices and avoiding common mistakes. Some key points to keep in mind include:
- Choosing a cryptographic library with a strong track record in security and performance.
- Ensuring proper key management and storage of private keys.
- Regularly updating cryptographic libraries to benefit from the latest security patches and improvements.
- Thoroughly testing the implementation to identify any vulnerabilities or loopholes.
- Seeking guidance from experts in the field or consulting reputable sources for additional insights and best practices.
Remember, the successful implementation of Schnorr Signature relies on a thorough understanding of its principles and diligent adherence to best practices.
FAQ
Q: What is Schnorr Signature?
A: Schnorr Signature is a digital signature scheme that provides secure and efficient means to sign and verify messages or transactions in cryptography.
Q: What are the advantages of Schnorr Signature?
A: Schnorr Signature offers enhanced security features, such as resistance against forgery and tampering, as well as improved efficiency and scalability compared to traditional signature schemes.
Q: Where is Schnorr Signature commonly used?
A: Schnorr Signature is widely used in blockchain technology for secure and efficient transaction verification. It is also employed in digital identity verification processes across various sectors.
Q: How can I implement Schnorr Signature?
A: Implementing Schnorr Signature involves generating a public-private key pair, signing the message using the private key, and verifying the signature using the corresponding public key.
Q: What are some common mistakes to avoid when implementing Schnorr Signature?
A: Common mistakes include choosing insecure cryptographic libraries, improper key management, lack of regular updates, and inadequate testing. Follow best practices and consult experts to avoid these pitfalls.
With this comprehensive guide, you are now equipped with a solid understanding of the power and potential of Schnorr Signature. Its enhanced security features, efficiency, and scalability make it a valuable asset in today's cybersecurity landscape. Whether you are involved in blockchain technology, digital identity verification, or any other field that requires secure digital signatures, Schnorr Signature is a game-changer. Embrace this revolutionary cryptographic algorithm and unlock endless possibilities in securing the digital world!
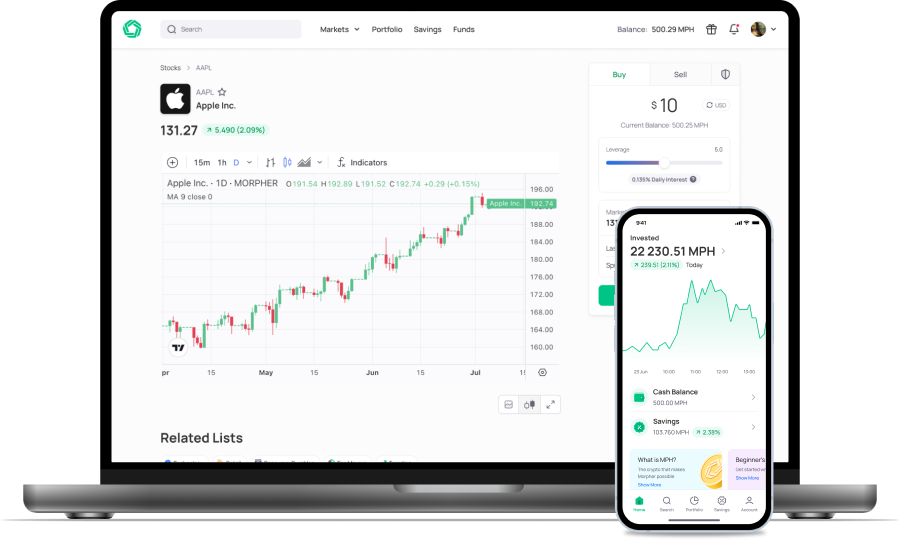
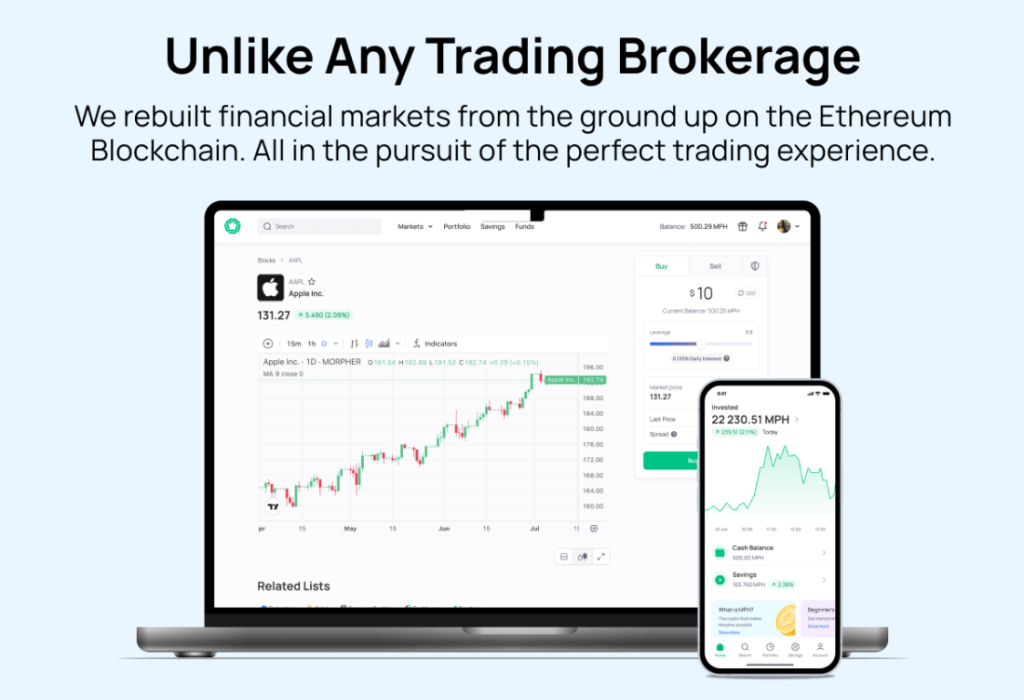
Ready to harness the power of Schnorr Signature in your trading endeavors? Look no further than Morpher, the revolutionary trading platform that integrates the security and efficiency of blockchain technology into every transaction. With Morpher, you can trade a wide array of assets, from stocks and cryptocurrencies to forex and unique markets, all with zero fees, infinite liquidity, and up to 10x leverage. Embrace the future of investing with a platform that offers fractional investing, short selling, and the safety of a non-custodial wallet. Sign Up and Get Your Free Sign Up Bonus today to experience a unique trading experience tailored for the digital age.
Disclaimer: All investments involve risk, and the past performance of a security, industry, sector, market, financial product, trading strategy, or individual’s trading does not guarantee future results or returns. Investors are fully responsible for any investment decisions they make. Such decisions should be based solely on an evaluation of their financial circumstances, investment objectives, risk tolerance, and liquidity needs. This post does not constitute investment advice.

Painless trading for everyone
Hundreds of markets all in one place - Apple, Bitcoin, Gold, Watches, NFTs, Sneakers and so much more.

Painless trading for everyone
Hundreds of markets all in one place - Apple, Bitcoin, Gold, Watches, NFTs, Sneakers and so much more.