Preventing Man-in-the-Middle Attacks

Man-in-the-Middle (MitM) attacks have become increasingly prevalent in today's digital landscape. In this comprehensive guide, I will delve into the world of MitM attacks, their impact, and most importantly, preventive measures to shield yourself from falling victim to these malicious tactics.
Understanding Man-in-the-Middle Attacks
Man-in-the-Middle attacks are a prevalent form of cyber threat that can have severe consequences for both individuals and organizations. These attacks occur when a malicious actor inserts themselves into a communication channel between two parties, allowing them to eavesdrop on and manipulate the data being exchanged. The unsuspecting parties believe they are communicating directly with each other, unaware that an intermediary is intercepting their messages.
Defining Man-in-the-Middle Attacks
Man-in-the-Middle attacks refer to the interception and alteration of communication between two parties, unbeknownst to either of them. The attacker positions themselves between the sender and the recipient, allowing them to gain unauthorized access to sensitive information. This unauthorized access can lead to a range of malicious activities, including identity theft, financial fraud, and espionage.
How Man-in-the-Middle Attacks Work
A typical MitM attack involves three key phases: interception, decryption, and re-encryption. Firstly, the attacker eavesdrops on the communication channel, intercepting the data being transmitted. Next, they decrypt the intercepted data to extract valuable information, such as credit card details or login credentials. Finally, to remain undetected, the attacker re-encrypts the data and delivers it to the intended recipient, ensuring the exchange appears genuine. It is essential for individuals and organizations to be vigilant against these attacks by implementing robust security measures such as encryption, digital signatures, and secure communication protocols.
The Impact of Man-in-the-Middle Attacks
Potential Risks and Damages
The impact of Man-in-the-Middle (MitM) attacks can be devastating, both on an individual and organizational level. MitM attacks occur when a malicious actor intercepts communication between two parties, allowing them to eavesdrop on sensitive information. Personal information, such as social security numbers and bank account details, can be compromised, leading to identity theft and financial loss. Additionally, hackers can manipulate the intercepted data, leading to unauthorized transactions and further financial harm. Furthermore, businesses risk reputational damage, as customer trust can be shattered if sensitive data falls into the wrong hands, potentially resulting in loss of clientele and revenue.
Industries Most Affected by Man-in-the-Middle Attacks
Although no industry is immune to MitM attacks, certain sectors are particularly vulnerable due to the exchange of highly sensitive information. Financial institutions, such as banks and investment firms, are prime targets for MitM attacks due to the vast amount of financial data they handle daily. Healthcare providers are also at high risk, as patient records and medical information are valuable targets for cybercriminals seeking to exploit vulnerabilities. Furthermore, e-commerce platforms face significant threats from MitM attacks, as they process a large volume of online transactions involving credit card details and personal information.
It is crucial for organizations in these industries to implement robust cybersecurity measures to mitigate the risks posed by MitM attacks. This includes encrypting data in transit, using secure communication protocols, and implementing multi-factor authentication to verify the identities of users. By staying vigilant and proactive in addressing cybersecurity threats, businesses can better protect themselves and their customers from the damaging effects of MitM attacks.
Key Techniques Used in Man-in-the-Middle Attacks
IP Spoofing
IP spoofing involves the attacker falsifying network packets to appear as if they originate from a trusted source. By manipulating IP addresses, the attacker can redirect traffic and intercept sensitive data.
One common scenario where IP spoofing is used is in Distributed Denial of Service (DDoS) attacks. By spoofing the source IP addresses in the attack packets, the target server is overwhelmed with an influx of traffic from various seemingly legitimate sources, making it difficult to filter out the malicious requests.
DNS Spoofing
DNS spoofing aims to manipulate the Domain Name System (DNS) cache, redirecting users to a malicious website instead of the intended destination. This technique enables attackers to gather login credentials, credit card information, or other sensitive data.
Another form of DNS spoofing is known as DNS cache poisoning, where the attacker injects false DNS records into a caching nameserver. This can lead to users being redirected to phishing websites or malware-infected pages without their knowledge.
HTTPS Spoofing
HTTPS spoofing occurs when the attacker creates a fraudulent website that appears secure by obtaining a valid SSL certificate. Users unknowingly access these imitation websites and disclose sensitive information, assuming they have a secure connection.
In some cases, attackers use a technique called SSL stripping, where they intercept HTTPS requests and downgrade them to insecure HTTP connections. This allows them to eavesdrop on the communication between the user and the website, potentially capturing login credentials or other confidential data.
Preventive Measures Against Man-in-the-Middle Attacks
Man-in-the-Middle (MitM) attacks pose a significant threat to the security of communication channels, making it imperative for individuals and organizations to implement robust preventive measures. By understanding the various strategies that can be employed to mitigate the risks associated with MitM attacks, you can better protect sensitive information and maintain the integrity of your data.
Encryption and Secure Protocols
Implementing strong encryption and utilizing secure protocols, such as HTTPS, is essential to safeguard your communication channels. Encryption encodes the transmitted data, rendering it unreadable to attackers, while secure protocols ensure a secure connection between parties. By encrypting data in transit and utilizing protocols that establish secure connections, individuals can significantly reduce the likelihood of falling victim to MitM attacks.
Furthermore, the use of digital certificates can enhance the security of communication channels by verifying the authenticity of parties involved in the data exchange. Digital certificates help establish trust between entities and ensure that the information is being transmitted securely without interception or alteration by malicious actors.
Multi-Factor Authentication
Implementing multi-factor authentication adds an extra layer of security by requiring users to provide multiple pieces of evidence to verify their identity. This mitigates the risk of unauthorized access, even in the event of compromised passwords. By incorporating factors such as biometric data, security tokens, or one-time passwords, organizations can bolster their authentication processes and reduce the susceptibility to MitM attacks.
Regular Software Updates
Frequently updating software and applications is crucial in preventing MitM attacks. Updates often include patches that address vulnerabilities identified by developers. Staying up to date ensures that you have the latest security measures in place. In addition to patching known vulnerabilities, software updates may also introduce new security features that enhance the overall resilience of systems against evolving threats like MitM attacks.
Advanced Security Measures
Intrusion Detection Systems
Intrusion Detection Systems (IDS) monitor network traffic and detect anomalies that may indicate a MitM attack. IDSs can automatically trigger alerts or even block suspicious activities, providing an additional layer of protection.
Security Information and Event Management
Security Information and Event Management (SIEM) solutions provide real-time monitoring, analysis, and correlation of security events across your network. By centralizing information from multiple sources, SIEM helps identify MitM attacks and other security threats.
As an expert in cybersecurity, I can't stress enough the importance of implementing preventive measures against Man-in-the-Middle attacks. Don't wait until it's too late to take action. By prioritizing security and adopting a multi-layered approach, you can significantly reduce the risk of falling victim to these insidious attacks.
Expert Tip: Always be cautious when connecting to public Wi-Fi networks. Cybercriminals often exploit unsecured networks to launch MitM attacks. Consider using a virtual private network (VPN) to encrypt your internet traffic and ensure secure communication.
FAQ
What is a Man-in-the-Middle attack?
A Man-in-the-Middle attack occurs when an attacker intercepts and alters communication between two parties, gaining unauthorized access to sensitive information without either party's knowledge.
How do Man-in-the-Middle attacks work?
Man-in-the-Middle attacks involve three main phases: interception, decryption, and re-encryption. The attacker eavesdrops on the communication, decrypts the intercepted data, and then re-encrypts it to appear genuine.
What industries are most vulnerable to Man-in-the-Middle attacks?
Industries that handle highly sensitive information, such as financial institutions, healthcare providers, and e-commerce platforms, are particularly vulnerable to Man-in-the-Middle attacks.
What are some preventive measures against Man-in-the-Middle attacks?
To protect against Man-in-the-Middle attacks, it is crucial to implement encryption and secure protocols, enable multi-factor authentication, and regularly update software. Advanced security measures like Intrusion Detection Systems and Security Information and Event Management solutions can also provide additional protection.
In conclusion, understanding the threat of Man-in-the-Middle attacks and taking proactive steps to safeguard your communication channels is crucial in today's interconnected world. By staying informed and implementing the preventive measures outlined in this guide, you can minimize the risk of falling victim to these malicious tactics.
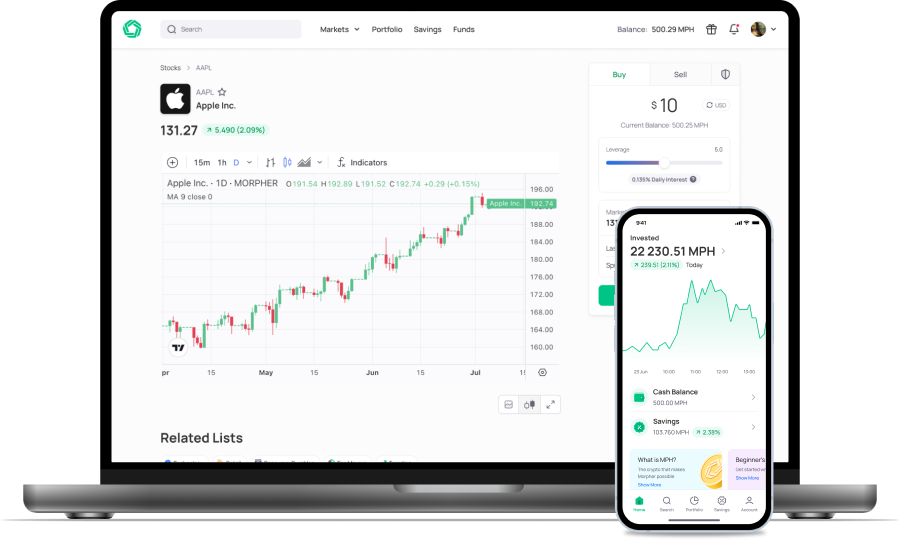
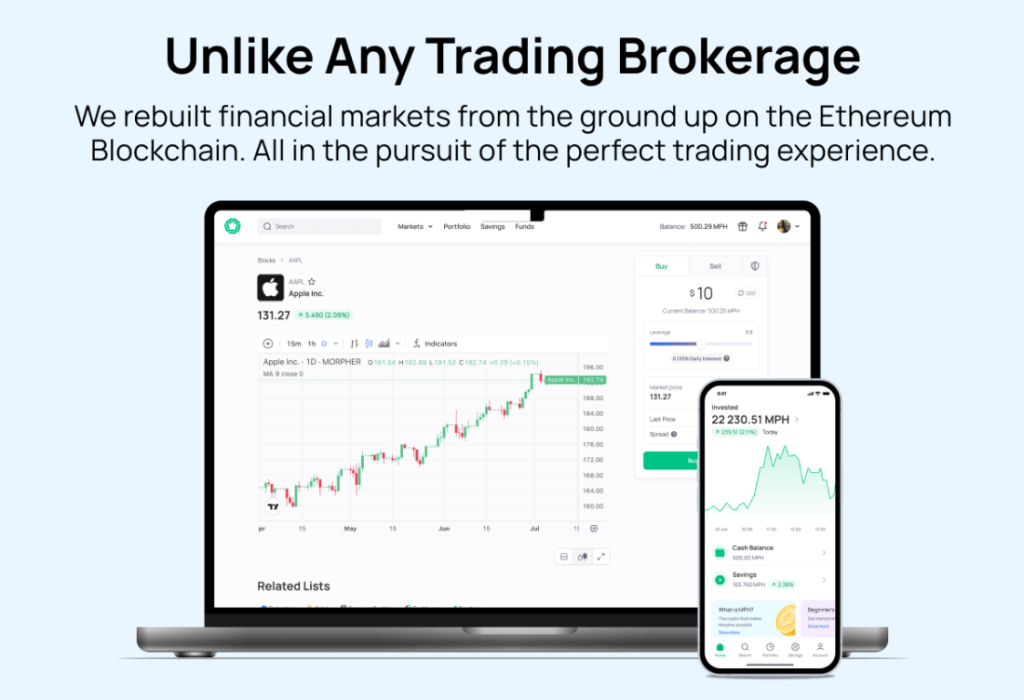
As you take proactive measures to protect against Man-in-the-Middle attacks, consider enhancing your trading experience with Morpher. Embrace the security and innovation of a platform that offers zero fees, infinite liquidity, and the safety of a non-custodial wallet. With Morpher, you can trade across a multitude of asset classes, enjoy the benefits of fractional investing, and even leverage your trades up to 10x. Ready to revolutionize your investing journey with a platform that's as secure as it is groundbreaking? Sign Up and Get Your Free Sign Up Bonus at Morpher.com today and join the future of trading.
Disclaimer: All investments involve risk, and the past performance of a security, industry, sector, market, financial product, trading strategy, or individual’s trading does not guarantee future results or returns. Investors are fully responsible for any investment decisions they make. Such decisions should be based solely on an evaluation of their financial circumstances, investment objectives, risk tolerance, and liquidity needs. This post does not constitute investment advice.

Painless trading for everyone
Hundreds of markets all in one place - Apple, Bitcoin, Gold, Watches, NFTs, Sneakers and so much more.

Painless trading for everyone
Hundreds of markets all in one place - Apple, Bitcoin, Gold, Watches, NFTs, Sneakers and so much more.