The Dangers of Spear Phishing: How to Protect Yourself

Spear phishing is a highly dangerous form of cyber attack that targets individuals and organizations alike. With the sophistication and prevalence of these attacks on the rise, it is crucial to understand the risks associated with spear phishing and take the necessary steps to protect yourself. In this article, I will provide you with an in-depth understanding of spear phishing, explain how it works, and offer practical tips for identifying and safeguarding against these malicious attacks.
Understanding Spear Phishing
Definition and Explanation of Spear Phishing
Spear phishing is a targeted attack strategy that aims to deceive individuals or organizations by masquerading as a legitimate and trustworthy communication. Unlike traditional phishing attempts, spear phishing takes personalized and customized approaches to trick victims into divulging sensitive information, such as login credentials, financial details, or intellectual property.
Spear phishing attackers prey on human psychology, exploiting our natural inclination to trust and our curiosity. By sending carefully crafted messages, often disguised as emails or instant messages, they manipulate recipients into taking specific actions or revealing confidential information.
The Evolution of Spear Phishing
Over the years, spear phishing techniques have become increasingly sophisticated. Cybercriminals leverage social engineering tactics and gather publicly available information to create highly convincing messages tailored to their victims. They might use information from social media profiles, corporate websites, or news articles to gain credibility and increase the likelihood of their targets falling for the bait.
Furthermore, with the rise of advanced hacking tools and automation, attackers can launch large-scale spear phishing campaigns, increasing the number of potential victims and maximizing their chances of success. So, even if you consider yourself cautious and vigilant, it's important to understand that spear phishing attacks can target anyone.
One of the key factors that contribute to the success of spear phishing attacks is the element of personalization. Attackers invest time and effort in researching their targets, gathering information that allows them to craft messages that appear genuine and relevant. They may study an individual's online presence, analyzing their social media activity, professional connections, and even personal interests. Armed with this knowledge, attackers can create messages that are tailored to the recipient's specific context, making it harder to discern the malicious intent behind them.
Moreover, spear phishing attacks often exploit current events or trends to increase their effectiveness. For example, during times of heightened anxiety, such as a global pandemic or a major political event, attackers may send emails claiming to provide important updates or resources related to the situation. By capitalizing on people's concerns and desire for information, these attackers manipulate their victims into opening attachments or clicking on links that lead to malware-infected websites.
It is also worth noting that spear phishing attacks are not limited to targeting individuals. Organizations, both small and large, are also prime targets for these attacks. Cybercriminals understand that by compromising the security of an organization, they can gain access to a wealth of valuable information, including customer data, trade secrets, and financial records. This knowledge has led to the development of spear phishing techniques specifically tailored to exploit vulnerabilities within corporate networks, such as sending emails that appear to come from high-ranking executives or trusted business partners.
The Risks Associated with Spear Phishing
Personal Information at Stake
Spear phishing poses a significant threat to your personal information. By tricking you into sharing sensitive details, attackers can gain access to your email accounts, social media profiles, bank accounts, and more. This can have severe consequences, leading to identity theft, financial loss, or even reputational damage.
Financial Implications of Spear Phishing
Spear phishing attacks can also have dire financial implications, both for individuals and businesses. If a cybercriminal gains access to your bank account or credit card information, they can make unauthorized transactions, drain your funds, or conduct fraudulent activities on your behalf. For organizations, the financial ramifications can be even more severe, with potential legal consequences and substantial financial losses.
How Spear Phishing Works
The Process of a Spear Phishing Attack
Spear phishing attacks typically follow a structured process. First, the attacker selects a target and gathers information about them. They might study their online presence, analyze their contacts, or monitor their activities to ensure they tailor their attack precisely. Once armed with this information, they create a personalized message designed to deceive the recipient.
The message usually contains elements that mimic familiar and trusted sources, such as a colleague, a client, or a service provider. It might request sensitive information, direct the recipient to a malicious website, or encourage them to download a malicious attachment. Once the recipient takes the desired action, the attacker gains unauthorized access to their systems or information.
Common Techniques Used by Cybercriminals
Spear phishing attackers employ a variety of techniques to make their messages convincing and increase the chances of success. They might spoof email addresses to appear as a trusted source, use social engineering tactics to create a sense of urgency, or even leverage psychological manipulation to exploit fears and anxieties. Moreover, they often take advantage of zero-day vulnerabilities in software or impersonate reputable companies to deceive their victims.
Identifying a Spear Phishing Attempt
Red Flags in Emails and Messages
Recognizing the signs of a spear phishing attempt is crucial for protecting yourself. Keep an eye out for suspicious email addresses, grammatical or spelling errors in the message, or unusual requests for personal information. Be cautious if the sender is urging you to act quickly or claiming that dire consequences will occur if you don't comply immediately.
Suspicious Links and Attachments
Always exercise caution when clicking on links or downloading attachments. Hover over links to see the actual URL before clicking, and if the domain looks suspicious or unfamiliar, refrain from proceeding. Similarly, be wary of unexpected file attachments, especially those ending in .exe or .zip, as they have the potential to contain malware or viruses.
Protecting Yourself from Spear Phishing
Implementing Strong Security Measures
To fortify your defenses against spear phishing attacks, it is crucial to implement robust security measures. This includes installing and regularly updating reliable antivirus software, enabling firewalls, and using spam filters to block suspicious emails. Additionally, consider employing advanced threat detection systems that can identify potential spear phishing attempts and prevent malicious activities.
The Role of Regular Software Updates
Regularly updating your software is another critical step in protecting yourself from spear phishing attacks. Developers frequently release patches and security updates designed to fix vulnerabilities that cybercriminals might exploit. By keeping your operating systems, applications, and plugins up to date, you minimize the risk of falling prey to spear phishing attempts that target known weaknesses.
Importance of User Awareness and Education
One of the most effective defenses against spear phishing is user awareness and education. Stay informed about the latest phishing techniques, learn to spot the signs of a spear phishing attempt, and educate yourself on best practices for online safety. Sharing knowledge and advice with your friends, family, or colleagues can collectively strengthen defenses and create a safer online environment.
As an expert in cybersecurity, I cannot stress enough the importance of maintaining a skeptical mindset and questioning the authenticity of every email or message you receive. Remember, even if a message appears legitimate, it's better to be safe than sorry.
Follow these steps to protect yourself and your personal information, and always stay informed about the latest spear phishing trends and preventive measures. By doing so, you are taking proactive steps to defend against the ever-present danger of spear phishing.
FAQs – Frequently Asked Questions
Q: What is spear phishing?
A: Spear phishing is a targeted cyber attack that involves sending personalized and convincing messages to deceive individuals or organizations into sharing sensitive information or taking specific actions, such as clicking on malicious links or downloading infected attachments.
Q: How can I identify a spear phishing attempt?
A: Look out for red flags in emails or messages, such as suspicious email addresses, grammar or spelling errors, or requests for personal information. Be cautious of urgent or threatening messages, and scrutinize links and attachments for any signs of suspicious activity.
Q: What can I do to protect myself from spear phishing?
A: Implement strong security measures, including antivirus software, firewalls, and spam filters. Regularly update your software to patch known vulnerabilities. Most importantly, stay informed about spear phishing techniques and educate yourself and others on best practices for online safety.
I once had a close encounter with a spear phishing attack when I received an email that seemed to be from my bank, asking me to update my account information urgently. Although the message looked genuine at first glance, something didn't feel right, so I called my bank's customer service to confirm if they had indeed sent the email. As it turned out, the email was a sophisticated phishing attempt, and I managed to avoid falling into the trap.
Always trust your instincts and take additional steps to verify the authenticity of suspicious messages. It could save you from falling victim to a spear phishing attack.
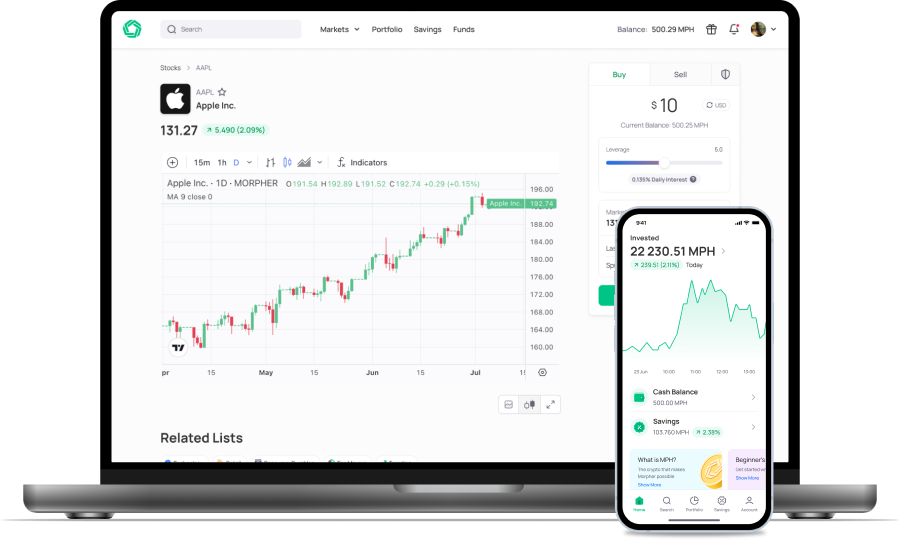
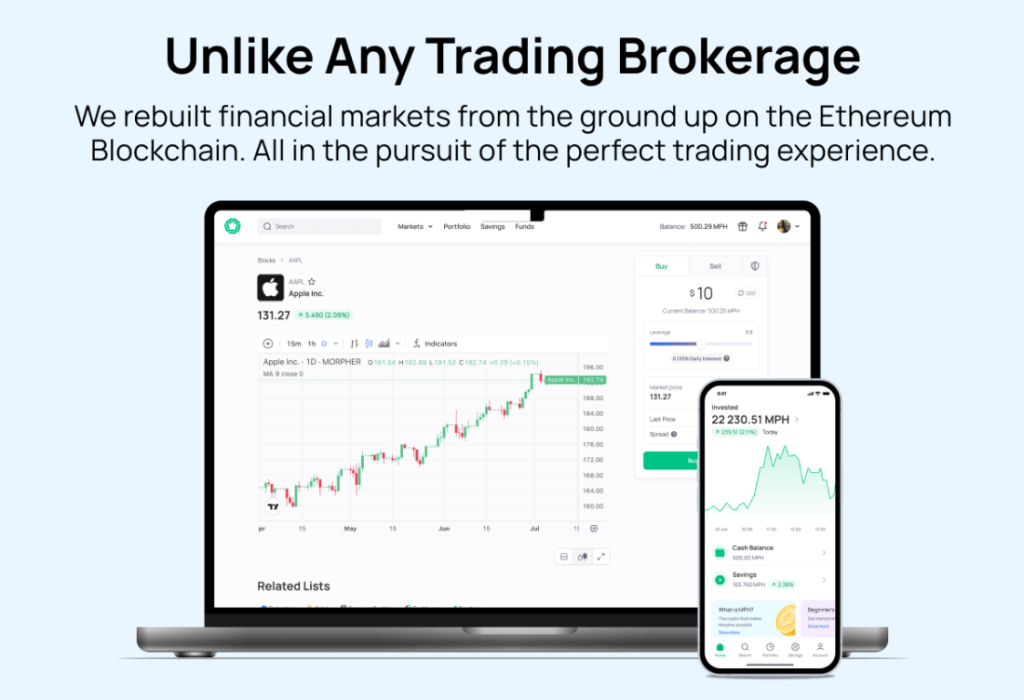
While staying vigilant against spear phishing is essential, it's equally important to ensure your investments are secure and efficient. Morpher.com offers a revolutionary trading platform that not only prioritizes user safety but also transforms the way you invest. With zero fees, infinite liquidity, and the ability to trade across multiple asset classes, Morpher empowers you to take control of your financial future. Embrace the innovative world of blockchain-based trading with fractional investing, short selling, and up to 10x leverage. Don't miss out on a unique trading experience with Morpher. Sign Up and Get Your Free Sign Up Bonus today and join the future of investing.
Disclaimer: All investments involve risk, and the past performance of a security, industry, sector, market, financial product, trading strategy, or individual’s trading does not guarantee future results or returns. Investors are fully responsible for any investment decisions they make. Such decisions should be based solely on an evaluation of their financial circumstances, investment objectives, risk tolerance, and liquidity needs. This post does not constitute investment advice.

Painless trading for everyone
Hundreds of markets all in one place - Apple, Bitcoin, Gold, Watches, NFTs, Sneakers and so much more.

Painless trading for everyone
Hundreds of markets all in one place - Apple, Bitcoin, Gold, Watches, NFTs, Sneakers and so much more.